The use of TLS certificates to secure and identify websites has dramatically expanded on the World Wide Web. This has been driven by browsers showing negative indicators for non-https sites, thus encouraging websites to use TLS. The screenshots below show Firefox’s and Chrome’s new indicator for sites that are not using a TLS certificate:
Figure 1: Firefox user display for not secure sites
Figure 2: Chrome user display for not secure sites
The Chrome display is much more prominent, but Firefox is expected to make their warning more explicit.
TLS certificates come in three flavors: Domain Validated (DV), Organizationally Validated (OV) and Extended Validation (EV). The basic differences are shown in the table below:

Table 1: Comparison of DV/OV/EV certificates
In all cases, encryption is provided between the browser and the server. However, encryption does not provide authentication. We know that the browser is encrypting data to some server with a verified domain name. But we know nothing about that domain with a DV certificate. With OV and EV, we are given more information about the domain, including the location of the business (OV), and even more details with EV.
With the advent of a web which is greater than 90% encrypted and with browsers showing a green padlock for all https sites regardless of the certificate type, it’s a fallacy to just “look for the lock,” as this is insufficient to protect users from fraudulent sites. Users must be diligent in looking for cues about the site’s identity. With EV certificates, most browsers will display the legal name of the company next to the URL in the address bar. This provides excellent visibility that the site has been authenticated.
Another clue to look for is the name of the Certificate Authority (CA) that issued the website’s certificate. With some browsers, users can hover over the lock to see the name of the CA. If the indicator says “Verified by DigiCert,” you can be sure that the site identification has been verified according to industry requirements. Leading CAs, such as DigiCert, are constantly updating the global standards by which CAs validate identities and follow rigorous processes. Look for a trusted name as the certificate issuer, such as in the figure below:
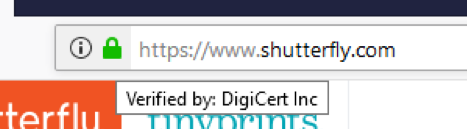
Figure 3: Hovering over URL in Firefox reveals the name of the issuing CA
OV and EV certificates require some effort to obtain. First, the requesting entity must be a valid organization and the CA must look at public registries to authenticate it. Because this involves manual labor, there is a cost associated with procuring the certificate. These are normally not obstacles for legitimate organizations. But for cybercriminals, they provide significant friction, which can be avoided by obtaining a DV certificate. Hence DV has become the certificate of choice for hackers and criminals.
Recent research showed that nearly half of phishing sites now have the padlock. Most often, DV certificates are successfully obtained for those websites. Hackers know they can automatically request DV without providing any personal information and they are offered for free by a few CAs. Hence not even a credit card is necessary. A recent report about a DNS compromise by an alleged nation-state claimed that hackers have concealed their operation by using “certificate impersonation,” obtaining certificates via Let’s Encrypt and Comodo (now known as Sectigo). Given the easy availability of these certificates, it’s no wonder cybercriminals are defaulting to DV to legitimize their websites.
What can consumers do to recognize fraudulent websites? Three words: examine, examine and examine.
- While it was OK in the past to just look for the lock, now the lock must be examined. Hover over the lock to see which CA issued the certificate. If it’s DigiCert, you can be sure that the website has been verified according to industry standards and that, in the case of an OV or EV certificate, the identity of the website owner has been vetted for added protection.
- Look closely at the address bar and read the address carefully. Is it what you expect?
- Does the company name show next to the lock, or is there a green bar? If so, and depending on the browser display, it’s an EV certificate and you can have high confidence that the website is authentic.
But what if the site is using a DV certificate? Does that mean it can’t be trusted? No, not necessarily. Again, take care to examine the items above. Millions of sites use DV and it’s perfectly fine for many applications. But e-commerce/financial transactions are not one of them.
Coming soon, look for more blogs such as:Qualified Certificates for PSD2
Distinguishing DV, OV and EV global industry requirements for validation
Potential enhancements to EV standards
Beyond the green bar: other benefits of high-assurance certificates for businesses